Browse our resources to explore the current best practices for validating storing and handling biological materials and how these techniques support data integrity and reproducibility.
Cell line authentication slideshare.
Authentication of a cell line is the sum of the process by which a line s identity is verified and shown to be free of contamination from other cell lines and microbes.
The lab directors and dna technicians at labcorp are highly experienced in providing the best possible cell line authentication and other research services to all of our clients including those around the world.
Using standardized techniques authentication enables communication among all users about the resource and ensures valid reproducible experimental results.
Cell lines cells that have been continually passaged over a long period of time and have acquired homogenous genotypic and phenotypic characteristics.
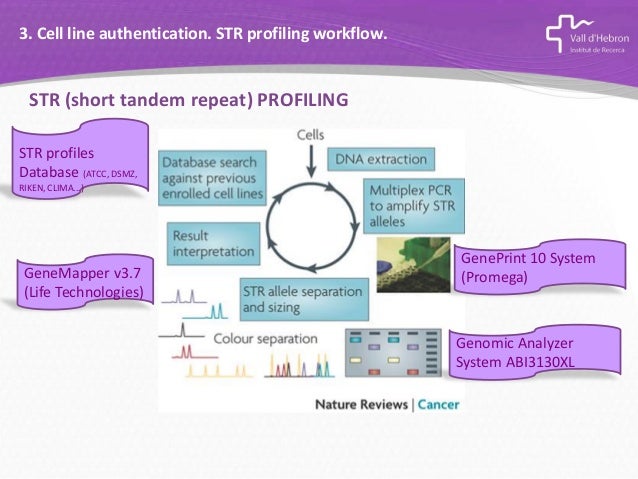
The geneprint 10 system provides a convenient str based method for cell line identity confirmation and for detection of intraspecies contamination in cultured human cell lines.
Animal cell culture and characterization of cell lines by cell morphology chromosome number banding and karyotyping etc.
They understand why their colleagues.
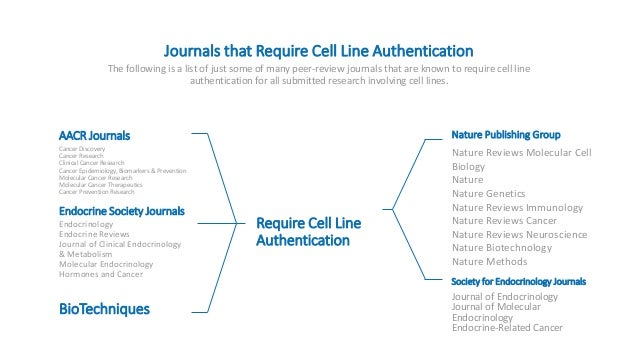
Do not include plans for the development and authentication of new key biological and or chemical resources such as a new human cancer cell line or a new antibody.
Applicants proposing to generate a new key biological and or chemical resource must describe the development and authentication of the resource in the approach section of the.
Further at the.
Our current clients include pharmaceutical and biotechnology companies universities cancer centers research hospitals and more.
Geneprint 10 coamplifies and detects nine human loci th01 tpox vwa amelogenin csf1po d16s539 d7s820 d13s317 d5s818 and d21s11 these loci collectively provide a genetic profile with a random match.
Cell line authentication can seem too time consuming or daunting.
Further the results can vary depending on the history of the cell line and the type of media used for cell growth.
Atcc is committed to improving the authentication of cell lines and microbial cultures.
Cell lines can be finite or continuous.
March 2015 isoenzyme analysis has been withdrawn until further notice.
An immortalized or continuous cell line has acquired the ability to proliferate indefinitely either through genetic mutations or artificial modifications.
Authentication i e confirmation that the cell line is not cross contaminated or misidentified confirmation of the species of origin correlation with the tissue of origin which.
For instance the code nhb 2 1 represents the cell line from normal human brain followed by cell strain or cell line number 2 and clone number 1.